Open source AI
incident response platform.
SOC Beacon ingests logs, runs YARA + Sigma rules, and enriches every alert with AI analysis and threat intelligence automatically.
Focused on alerting and detection for high-severity events — not a visibility or threat hunting suite.
No $50K/yr enterprise contract. No week-long onboarding. Just open source incident response workflows your analysts can use on day one.
SOC Beacon
Open source AI incident response
The problem
Full-visibility platforms cost $50K+ per year and take months to configure.
Your analysts still drown in uncontextualized alert noise.
An incident response stack for alerting and detection.
Open source. Self-hosted. Free.
Every capability a lean SOC team needs — from ingestion to AI enrichment to closed incident — in one self-hosted workflow.
Log Ingestion
Every log. Every source.
REST API and syslog ingestion with API key auth. Single-log and batch support. Raw messages are parsed and normalized automatically — no manual field mapping required.
AI Enrichment
4 AI analysts. Per alert. Automatically.
Multi-agent analysis gives every alert a scored, multi-perspective investigation before your analyst opens it. Defaults to gpt-4.1-nano to keep costs near zero.
Alert Triage
Close more incidents, faster.
Verdict and status workflow baked in. Mark alerts malicious, suspicious, or false positive. Track status from unassigned to resolved without leaving the dashboard.
Threat Intelligence
IOC context, zero API keys required.
Built-in enrichment for IPs, domains, URLs, and file hashes from open sources — no registration needed. Add key-based premium feeds when you're ready.
Detection Engines
YARA + Sigma. Out of the box.
Load your own YARA and Sigma rule sets with a configurable path. Toggle individual rules on or off. Detection runs at ingestion — no separate pipeline needed.
Scoring & Analytics
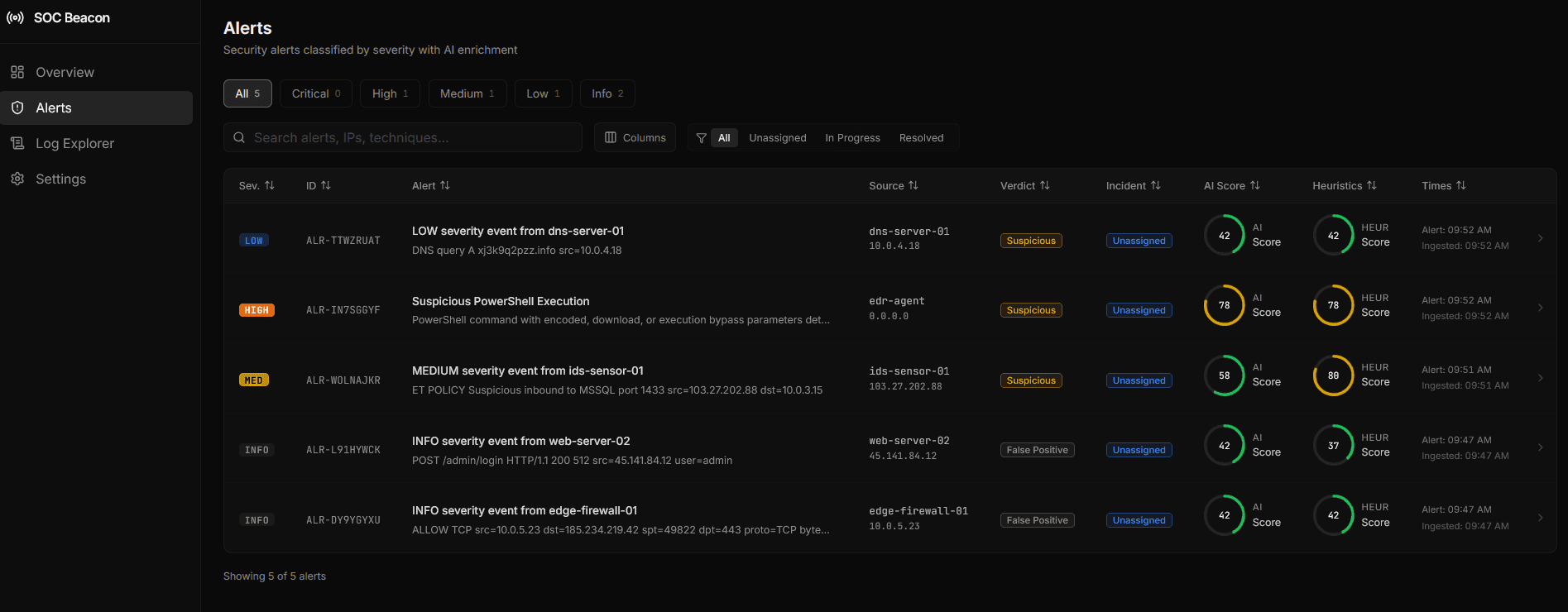
AI score + heuristics. Per alert.
Every alert gets an AI Score and Heuristics Score displayed as visual ring indicators. High = red. Low = green. Sortable, filterable columns for high-volume queues.
Built for analysts who need clarity.
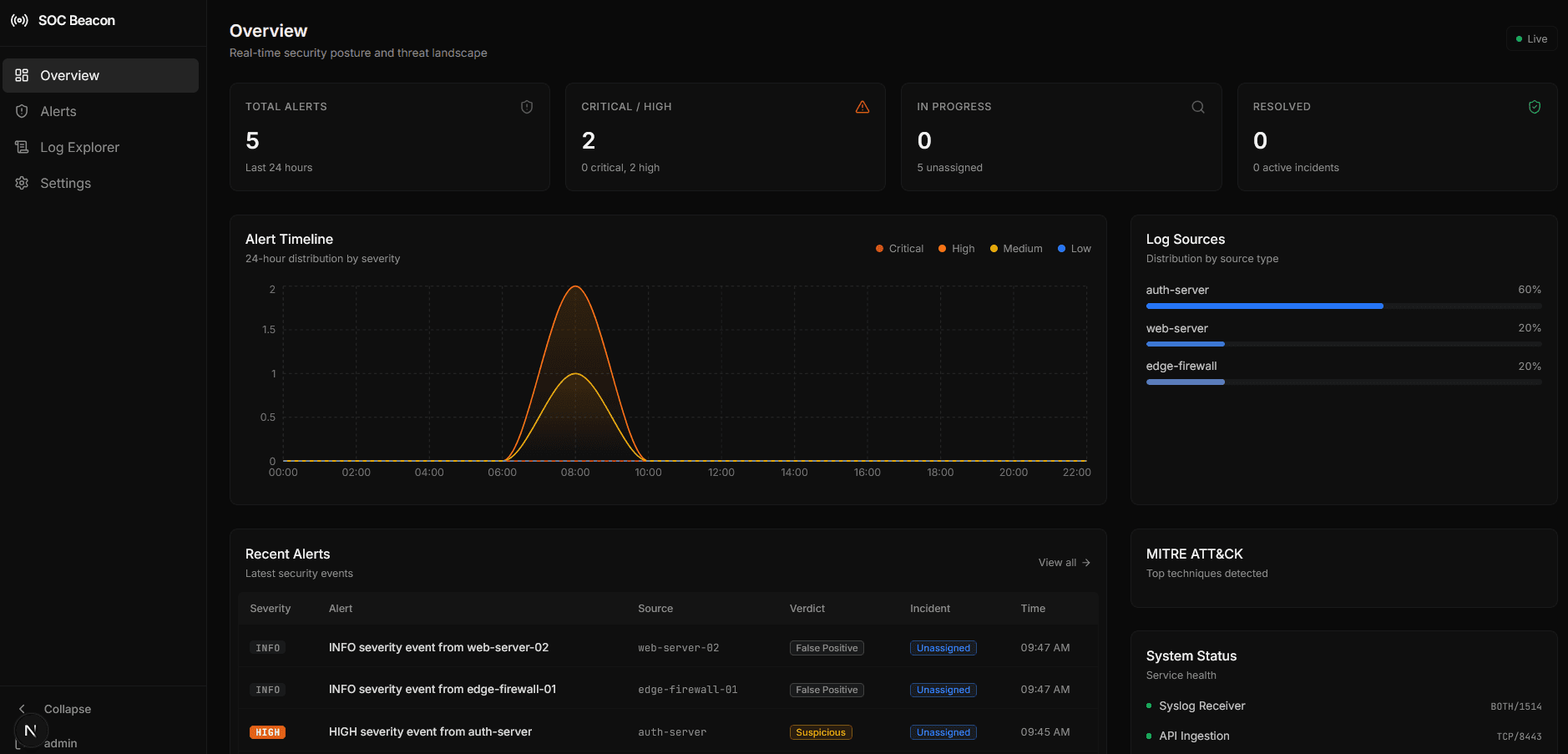
Real SOC workflows in a clean, fast UI. The screenshots below are pulled directly from the dashboard.
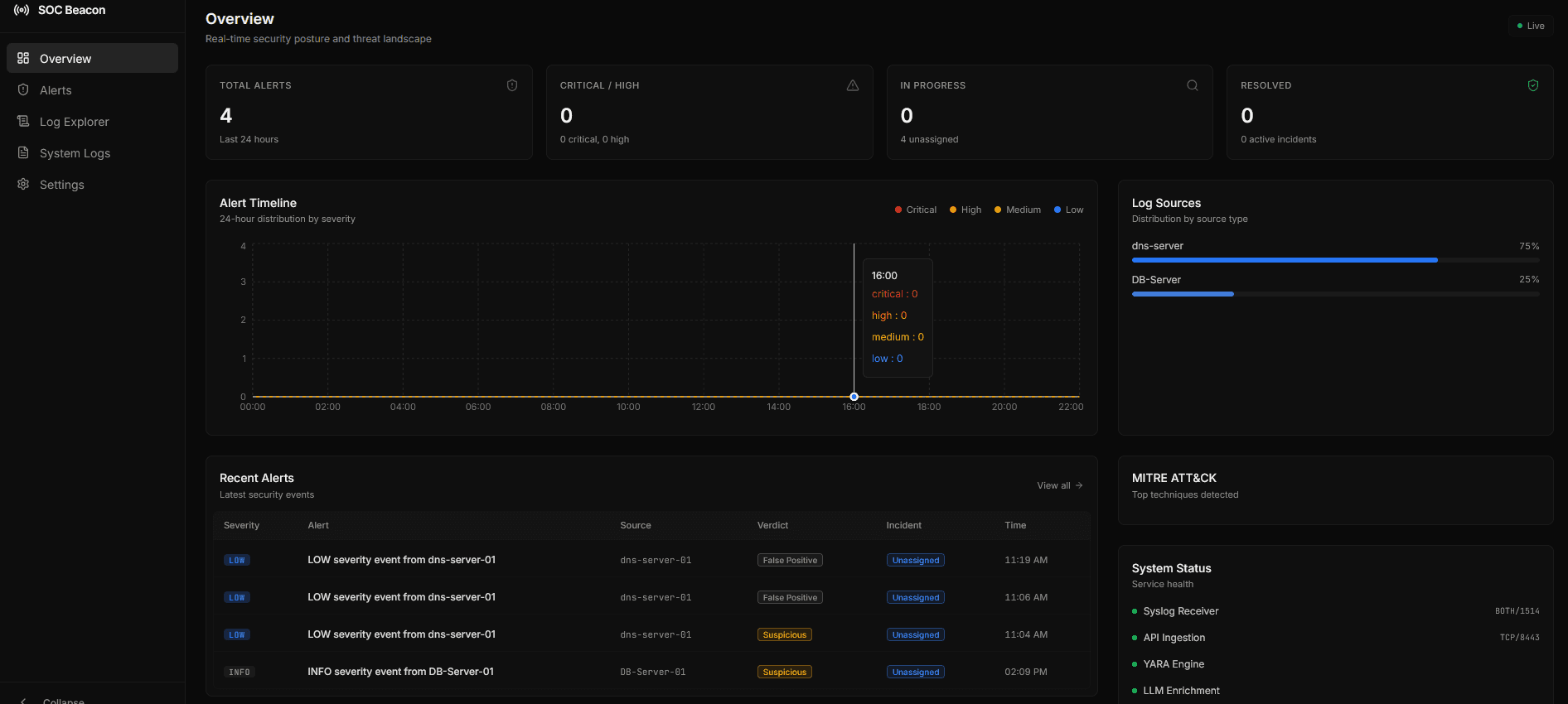
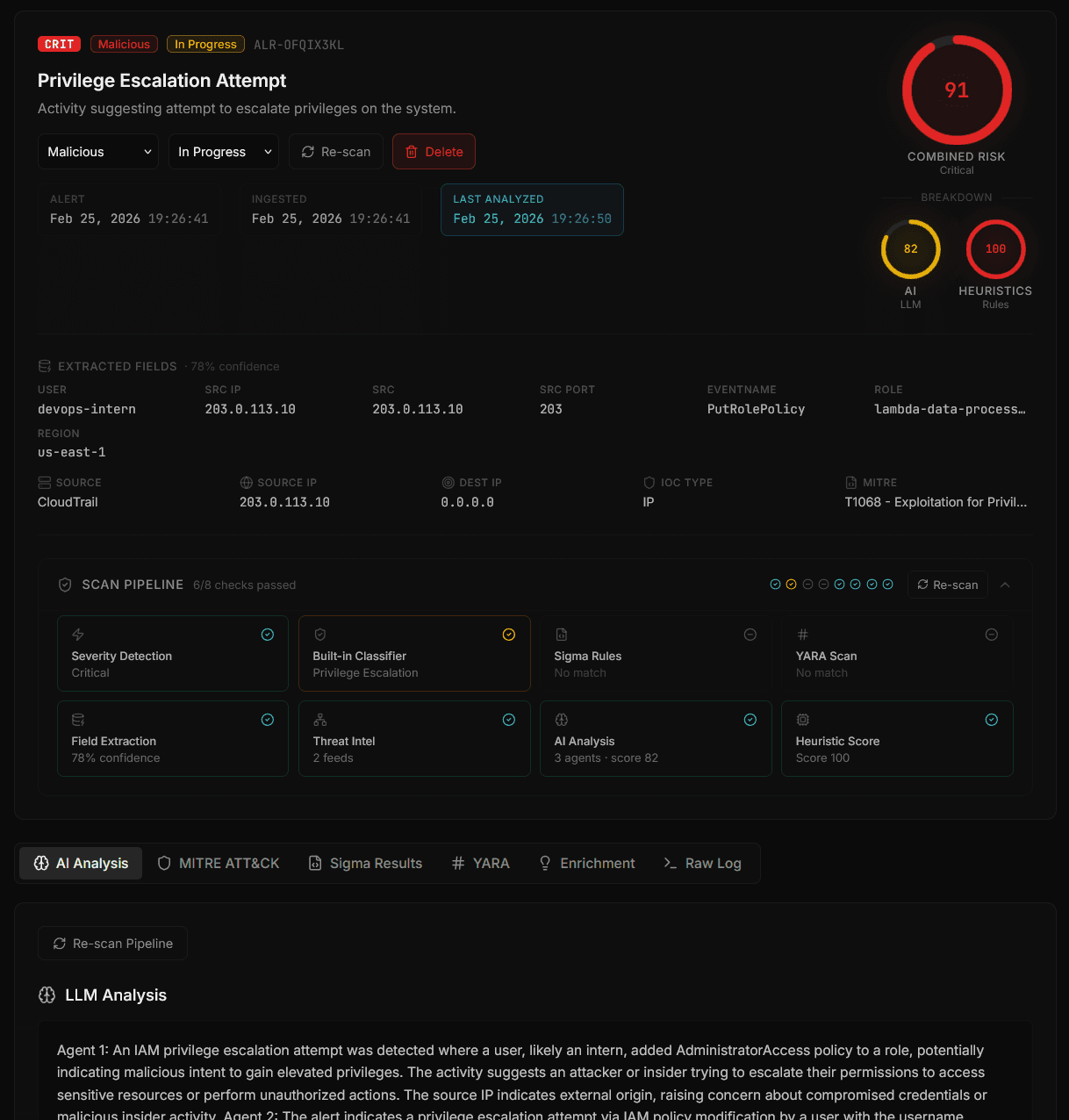
Unified Alert Console
One queue, scored by AI and heuristics, with instant verdicting.
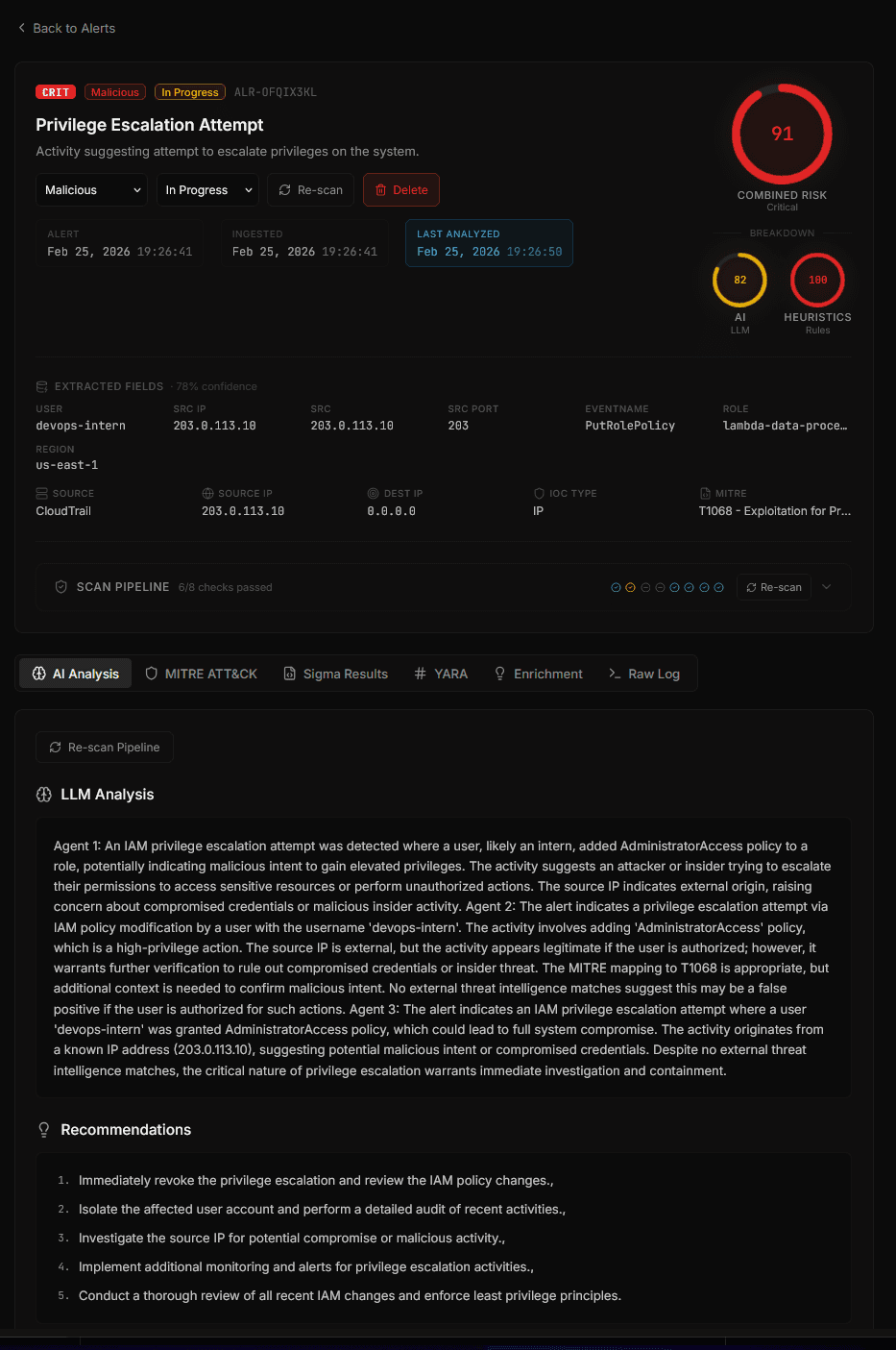
Alert Detail View
Tabs for raw logs, MITRE context, and intel enrichment.
AI Analyst Notes
Multi-agent summaries with confidence and recommended actions.
IOC Intelligence
IP, domain, and hash lookups inline — no API keys required.
From raw log to
closed incident.
Four automated stages turn event noise into actionable intelligence your team can act on immediately.
Ingest
Logs arrive via REST API or syslog. Each event is parsed, normalized, and stored with severity metadata extracted or inferred from the raw message.
Classify
The detection engine runs YARA and Sigma rules against each event. Alert is generated with MITRE ATT&CK mapping, severity, and baseline metadata.
Enrich
Threat intelligence lookups run on IPs, domains, and hashes. Then AI agents (1–4 perspectives) analyze the alert and produce scored findings with recommended verdict.
Triage
Analysts review enriched alerts in the dashboard — AI score, heuristics score, MITRE context, threat intel, and raw log all in one tabbed view. Set verdict and close.
Questions teams ask before they deploy.
Clear positioning on what SOC Beacon is and is not, plus key capability answers for evaluators.
Is SOC Beacon a full SIEM?
SOC Beacon focuses on alerting and detection workflows with AI enrichment. It is not positioned as a full visibility or threat hunting SIEM.
What is an AI incident response platform?
It ingests security events, runs detections, enriches alerts with AI and threat intelligence, and helps analysts triage incidents faster.
Is SOC Beacon open source?
Yes. SOC Beacon is open source and self-hosted under the MIT License.
Does it support YARA and Sigma rules?
Yes. You can load YARA and Sigma rule sets to detect malicious activity during ingestion.
Everything enterprise incident response platforms charge
$50,000/yr for.
You get all of it. Open source. Self-hosted. No vendor. No contract. Deploy today.
AI alert enrichment
Multi-agent, runs automatically
Threat intelligence lookups
IPs, domains, hashes — no API key
YARA + Sigma detection
Load your own rule sets
MITRE ATT&CK mapping
Per alert, auto-generated
Analyst triage dashboard
Verdict + incident status workflows
Self-hosted deployment
Your infra, your data
Vendor lock-in
Because it's open source
Ready to deploy?
Your incident response stack goes live today.
Not next quarter.
Clone the repo, add your OpenAI key, point your log sources at the API endpoint, and you're running a full AI-enriched alerting workflow.
git clone https://github.com/PolGs/soc-beaconNo account required · No credit card · No cloud dependency · MIT License